How to spot a phishing email
Phishing emails are getting harder to spot. Here is what to look for, with real UK examples of the tricks scammers use most often.
The email looks completely legitimate. It has the right logo, uses your name, references your account, and tells you something urgent needs your attention. The link it contains goes somewhere that looks like the real website. A few people click it every day, and a few of those people end up with a compromised account or money taken from them. Phishing emails are the single most common method used to steal personal data and financial information from ordinary people in the UK, and they have become significantly harder to spot than they were ten years ago.
The term phishing comes from the idea of baiting a hook and waiting for someone to bite. The email is the bait. What the sender wants varies: sometimes it is your login credentials, sometimes your banking details, sometimes access to your email account so they can target your contacts. The common thread is deception, and the craft behind it has improved considerably.
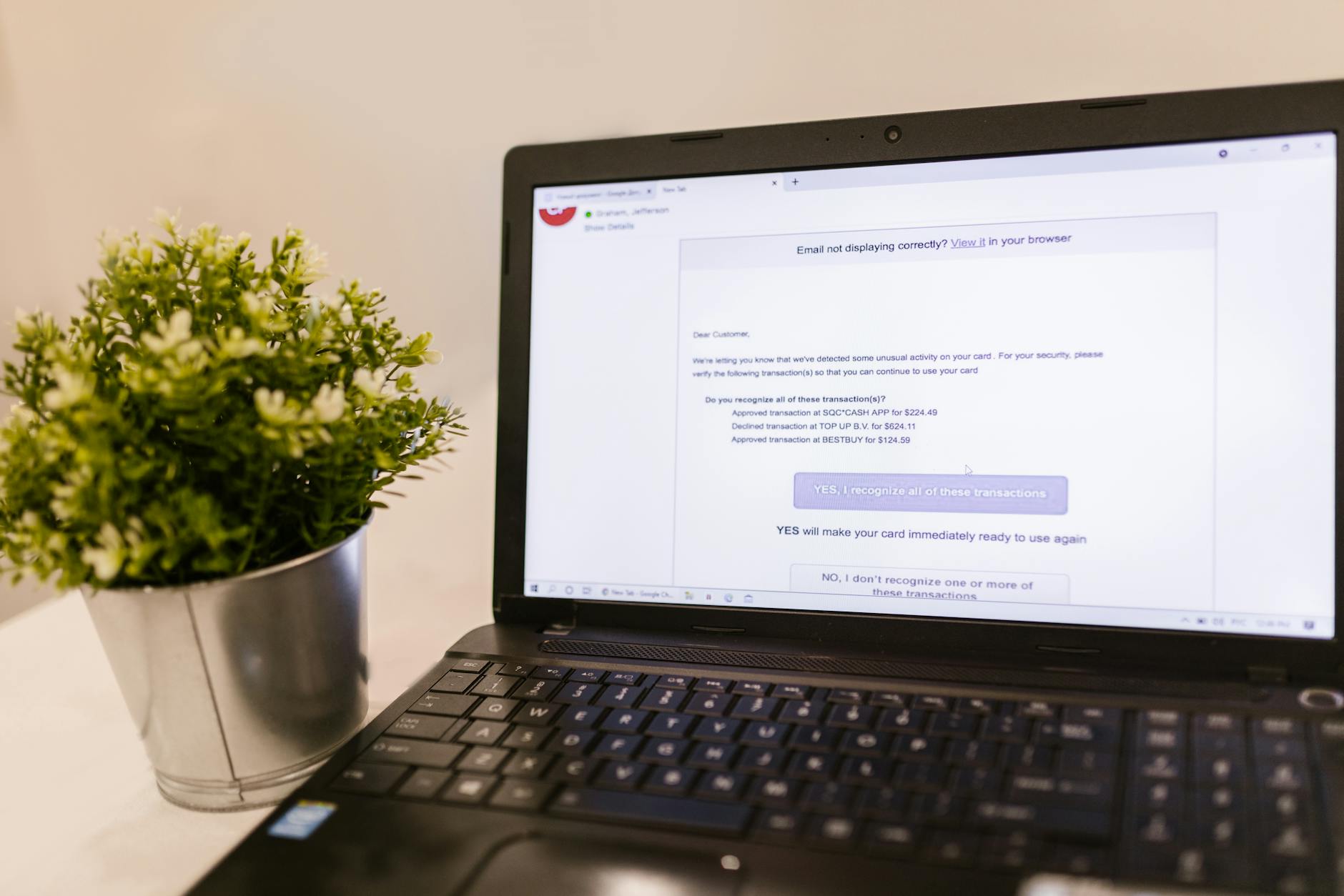
The most reliable thing you can do is slow down before you click anything. Phishing emails are almost always designed to create a sense of urgency. Your account has been suspended. There is unusual activity on your card. Your parcel could not be delivered. A payment has failed. The urgency is deliberate: it is designed to make you act before you think. The more alarmed the email makes you feel, the more carefully you should read it.
The sender address is the single most useful thing to check, and most people do not bother. The display name might say HMRC or Lloyds Bank or Amazon, but the actual email address tells you who really sent it. In a real email from HMRC, the address will end in @hmrc.gov.uk. If you see something like hmrc-refund@taxservicesuk.com, or noreply@amazon.account-update.net, that is not Amazon or HMRC. The domain name is what matters. Check it carefully, because some phishing addresses use close variations: amaz0n.com rather than amazon.com, or lloydsbankplc.com rather than lloydsbank.co.uk.
UK phishing emails often reference specific services that are genuinely common in British life. Royal Mail parcel notifications, HMRC tax refunds, TV Licence renewals, National Insurance number alerts, BT and Sky broadband bills, and NHS appointment confirmations are all templates that criminals use because millions of people have a relationship with these services and many will assume the email is real. The fact that the email references something you actually use is not evidence that it is genuine.
Hover over any link before you click it. On a desktop computer, you can move your cursor over a hyperlink and the actual destination URL will appear in the bottom corner of your browser. If the link text says “click here to verify your account” but the URL that appears is a string of numbers or an unfamiliar domain name, do not click it. On a phone this is harder, but you can hold your finger on a link to see where it goes before opening it. If you are ever unsure, go directly to the organisation’s website by typing the address yourself rather than following the link in the email.
Grammar and spelling are no longer the reliable tells they once were. The era of poorly written scam emails full of obvious errors is largely over. Modern phishing emails are often well-written and indistinguishable in tone from the real thing. That said, it is still worth reading carefully. Small oddities in phrasing, extra spaces, awkward word choices, and generic greetings like “Dear Customer” rather than your actual name can all indicate something is off. Legitimate organisations that have your details will usually address you by name.
Attachments should always be treated with suspicion. If an email you were not expecting comes with a document attached, the safest approach is to not open it. Malicious attachments can install software on your computer the moment they are opened, before you have even had a chance to read the contents. If a genuine organisation genuinely needs you to receive a document, there will almost always be another way to access it: logging into your account on their website, for instance.
When an email asks you to confirm personal information, that is a significant red flag. Legitimate organisations, including banks and government departments, do not ask you to verify your password, national insurance number, or banking details by email. If your bank genuinely needed to speak to you about something urgent, they would call you at the number they hold on file or ask you to log in through their app or website. An email asking you to type your password somewhere is never a legitimate request from a real organisation.
Two steps that cost nothing but time are worth building into a habit. The first is to check with the organisation directly if you are ever unsure. Ring the number on their official website, not a number provided in the email itself. The second is to report phishing emails rather than just deleting them. In the UK, you can forward suspicious emails to report@phishing.gov.uk, which is run by the National Cyber Security Centre. Each report helps them track active campaigns and take down fraudulent websites faster.
The people who get caught by phishing emails are not careless or naive. They are busy, they are stressed, and the email arrived at the wrong moment. The best protection is not to assume you will notice the signs instinctively, but to build a small habit of pause and check into how you handle your inbox. Slow down when something feels urgent. Look at the sender address properly. Hover before you click. And if something still does not feel right, go directly to the source rather than trusting the link you were given.